Digital Trust Is a Make or Break for Your Business
In today’s digital world where most business is done online, and data breaches are becoming more common, digital trust has become a valuable commodity for those companies that earn it.

In today’s digital world where most business is done online, and data breaches are becoming more common, digital trust has become a valuable commodity for those companies that earn it.

Tri-Paragon’s Acronis Cyber Protect Cloud has features that map to the National Institute of Standards and Technology’s (NIST) security framework, combines the most needed security, policy management, and data protection technologies in one platform.

Did you know?
Phishing is a type of online scam where an attacker impersonates legitimate organizations via email, text message or advertisement to trick a victim into revealing sensitive information to the attacker, or to deploy malicious software on the victim’s infrastructure.

Data protection is the process of safeguarding important information from corruption, compromise, or loss. The importance of data protection increases as the amount of data created and stored continues to grow at unprecedented rates. There is also little tolerance for downtime that can make it impossible to access important information.

Backup and recovery is the process of duplicating data and storing it in a secure place in case of loss or damage, and then restoring that data to a location — the original one or a safe alternative — so it can be again used in operations. Ideally, this backup copy (often called a snapshot) is immutable meaning it cannot be altered after it is created to protect against mutations such as ransomware.

Block email threats – including spam, phishing, business email compromise (BEC), malware, advanced persistent threats (APTs), and zero-days – before they reach end- users’ Microsoft 365, Google Workspace, Open-Xchange, or on-premises mailboxes.

Ransomware attacks, which pose a direct threat to user data, continue to grow in frequency and complexity. You may have heard of 2017 global epidemics such as WannaCry and exPetr, which hit hundreds of companies around the globe. Good news: We have Acronis Active Protection to keep your data safe and secure.

Prevent downtime and data loss with essential cyber protection from Tri-Paragon

Data protection is the process of securing digital information while keeping data usable for business purposes without trading customer or end-user privacy. Data protection is becoming more intricate as the number of devices to monitor and protect expands. Today, it includes IoT devices and sensors, industrial machines, robotics, wearables, and more. Data protection helps reduce risk and enables a business or agency to respond quickly to threats.
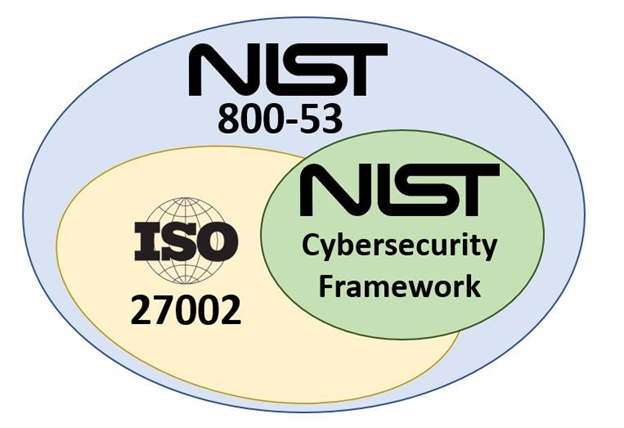
Here is what you need to know about the NIST’s Cybersecurity Framework. The tech world has a problem: security fragmentation. There is no standard set of rules–or even language–used to address the growing threats of hackers, ransomware, and stolen data, and the threat only continues to grow.